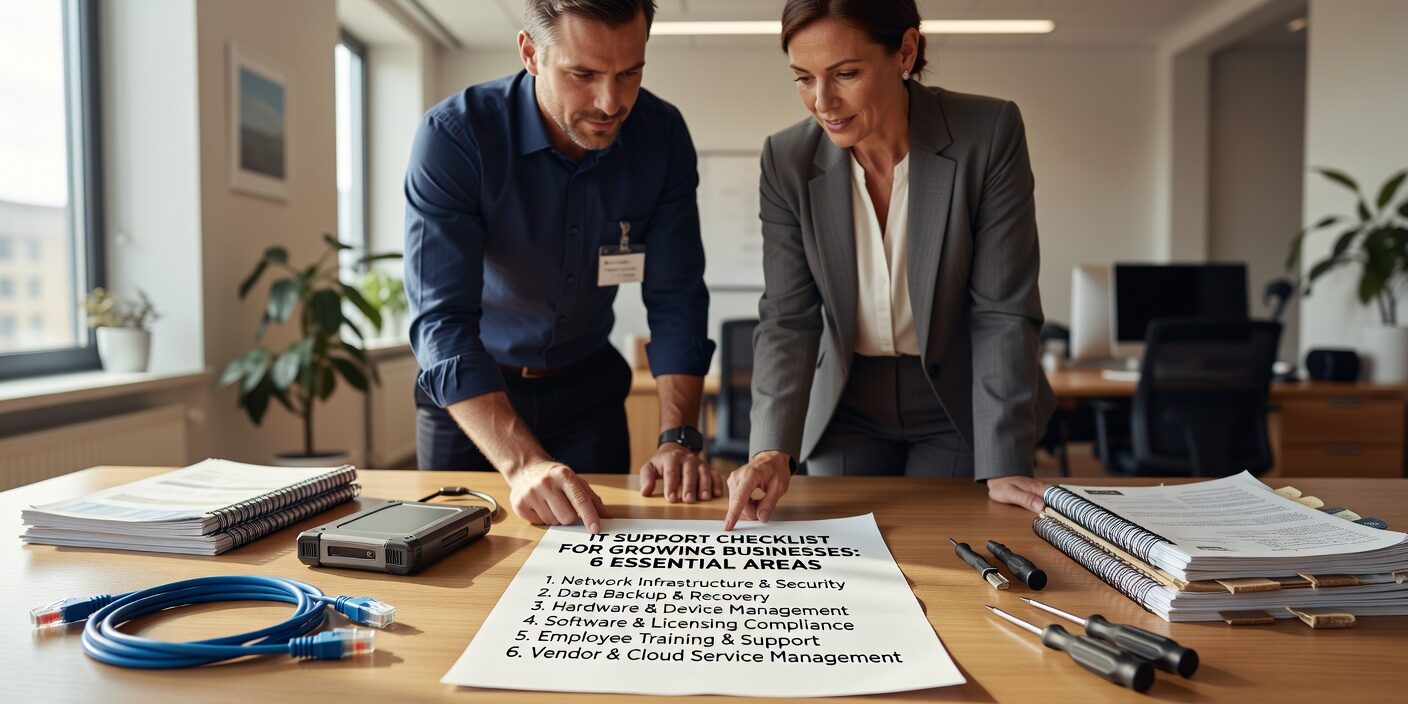
Growing businesses face a critical challenge: their IT needs evolve faster than their resources. Without a comprehensive IT support checklist for growing businesses, companies often discover gaps at the worst possible moment—during system failures, security incidents, or when trying to scale operations quickly.
The difference between businesses that thrive during growth and those that struggle often comes down to proactive IT planning. This checklist covers six essential areas that every growing business must address to maintain operational efficiency, protect against security threats, and build a foundation for sustainable expansion.
Infrastructure Assessment and Documentation
Before you can improve your IT support, you need to understand what you currently have. A complete technology inventory serves as the foundation for all future planning and troubleshooting efforts.
Start by documenting every piece of hardware, software license, and network component in your environment. Include purchase dates, warranty information, and planned replacement schedules. This documentation becomes invaluable when planning capacity upgrades or responding to equipment failures.
Evaluate your current capacity against your growth projections. Can your servers handle twice the current workload? Is your network bandwidth sufficient for additional remote workers? Most growing businesses discover they need infrastructure upgrades every 12 to 18 months.
Key infrastructure priorities include:
• Server performance and storage capacity • Network bandwidth and wireless coverage • Cloud service integrations and data flow • Hardware refresh schedules and budgeting • Scalability planning for 2-3x growth scenarios
Help Desk Protocols and Response Procedures
Effective help desk protocols directly impact employee productivity and customer satisfaction. Structured support procedures ensure consistent response times and proper issue escalation, regardless of who handles the initial request.
Establish clear response time expectations based on issue severity. Critical system outages requiring immediate attention, while routine password resets can be handled within standard business hours. Document these expectations and communicate them to your team.
Implement a ticket tracking system to monitor resolution times, identify recurring problems, and measure user satisfaction. Many growing businesses discover that certain issues repeat frequently, indicating underlying problems that need permanent solutions rather than ongoing fixes.
Response time framework:
• Critical issues (system down, security breach): 15-30 minutes • High impact (multiple users affected): 2-4 hours • Standard requests (single user problems): Same business day • General inquiries (training, how-to): 24-48 hours
For businesses with fewer than 25 employees, outsourcing help desk functions often provides better coverage and expertise than hiring full-time IT staff.
Proactive Network Monitoring
Reactive IT support costs significantly more than proactive monitoring. 24/7 network monitoring catches potential problems before they impact operations, reducing both downtime and emergency repair costs.
Modern monitoring tools track server availability, bandwidth utilization, application response times, and security threats in real-time. Automated alerts notify IT teams when performance metrics exceed established thresholds, enabling quick intervention.
Schedule regular maintenance windows for applying patches, reviewing system logs, and optimizing performance. Most businesses find that monthly maintenance prevents the majority of unexpected system issues.
Essential monitoring areas:
• Server and application availability • Network bandwidth and latency • Storage capacity and backup status • Security threats and anomalies • User activity and access patterns
Cybersecurity Measures and Compliance
Cybersecurity threats target growing businesses specifically because they often have valuable data but limited security resources. Layered security defenses protect against multiple attack vectors while maintaining usability for employees.
Implement multi-factor authentication across all business applications and email systems. This single step prevents the majority of account compromise attempts, even when passwords are stolen or guessed.
Conduct regular vulnerability scans and employee security training. Many successful attacks exploit known vulnerabilities or rely on employee mistakes. Quarterly security assessments help identify and address weaknesses before they’re exploited.
Core security protocols:
• Multi-factor authentication for all accounts • Regular vulnerability scanning and penetration testing • Employee security training and phishing simulations • Incident response plan with documented procedures • Compliance verification for industry regulations
Develop and test an incident response plan annually. Knowing exactly what to do during a security event reduces both damage and recovery time.
Backup and Disaster Recovery Procedures
Reliable backup and disaster recovery procedures protect business continuity when unexpected events occur. Many growing businesses discover backup problems only when they need to restore critical data.
Implement the 3-2-1 backup rule: maintain three copies of important data, store them on two different media types, and keep one copy offsite or in the cloud. Test backup integrity monthly by performing actual restore operations.
Define recovery time objectives for different business functions. Email systems might need restoration within four hours, while financial databases may require 30-minute recovery times. These targets guide technology investments and procedure development.
Recovery planning essentials:
• Daily automated backups with 30-90 day retention • Monthly full restore testing and verification • Documented recovery procedures for different scenarios • Communication plans for extended outages • Remote work capabilities for staff continuity
Ransomware protection requires particular attention, as these attacks specifically target backup systems. Maintain offline or immutable backup copies that cannot be encrypted by malware.
Technology Planning and Vendor Management
Proactive technology planning aligns IT investments with business growth objectives. Strategic planning prevents reactive spending and ensures technology supports rather than constrains business expansion.
Develop a 12-24 month technology roadmap that coordinates infrastructure upgrades, security improvements, and vendor contract renewals. This approach spreads costs over time and reduces the likelihood of emergency purchases.
Regularly evaluate vendor performance against service level agreements. Track response times, resolution rates, and customer satisfaction scores. Poor vendor performance impacts your entire operation, making regular assessment critical.
Planning priorities by quarter:
• Q1: Infrastructure assessment and capacity planning • Q2: Security audits and compliance verification • Q3: Cloud optimization and integration projects • Q4: Vendor performance reviews and contract renewals
Budget 15-20% above projected IT expenses for unexpected needs. Growing businesses often encounter technology requirements that weren’t anticipated during initial planning.
Negotiate specific performance guarantees in vendor contracts, including uptime commitments, response times, and escalation procedures. These agreements become essential when service problems impact business operations.
What This Means for Your Business
Implementing a comprehensive IT support checklist transforms technology from a potential liability into a business advantage. Companies that address these six areas proactively experience fewer disruptions, stronger security, and more predictable technology costs.
Start with a complete assessment of your current environment, then prioritize high-risk areas like cybersecurity and backup procedures. Consistent quarterly reviews and monthly maintenance activities prevent most IT problems before they impact operations.
The investment in proper IT support planning pays dividends through reduced downtime, improved employee productivity, and the confidence to pursue growth opportunities without technology constraints.
Many growing businesses successfully double their revenue without experiencing IT meltdowns by following structured approaches like this checklist. The key lies in consistent execution and regular review of your technology environment.
For businesses seeking expert guidance on implementing these IT support best practices, managed IT support for growing businesses can provide the expertise and resources needed to build a robust, scalable technology foundation. Professional IT support ensures your business has the reliability, security, and performance needed to support continued growth and success.